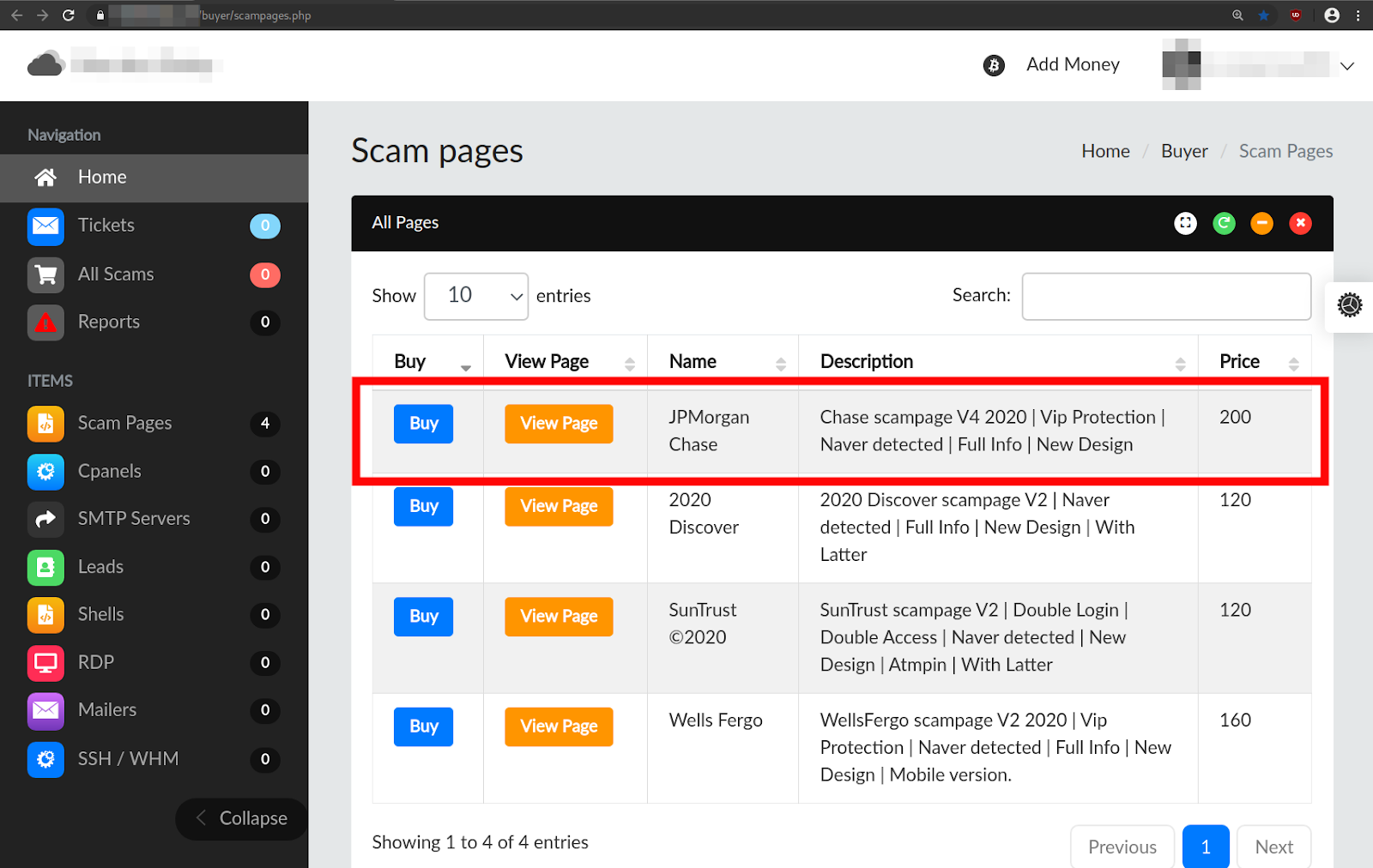
Catching the big fish: Analyzing a large-scale phishing-as-a-service operation | Microsoft Security Blog
![Phishing kit] Coinbase phishing kit with live admin panel to bypass MFA – an analysis. – StalkPhish – phishing and brand impersonation detection Phishing kit] Coinbase phishing kit with live admin panel to bypass MFA – an analysis. – StalkPhish – phishing and brand impersonation detection](https://stalkphishhome.files.wordpress.com/2023/01/coinbase-mfa-kit_analysis.png?w=1084)
Phishing kit] Coinbase phishing kit with live admin panel to bypass MFA – an analysis. – StalkPhish – phishing and brand impersonation detection

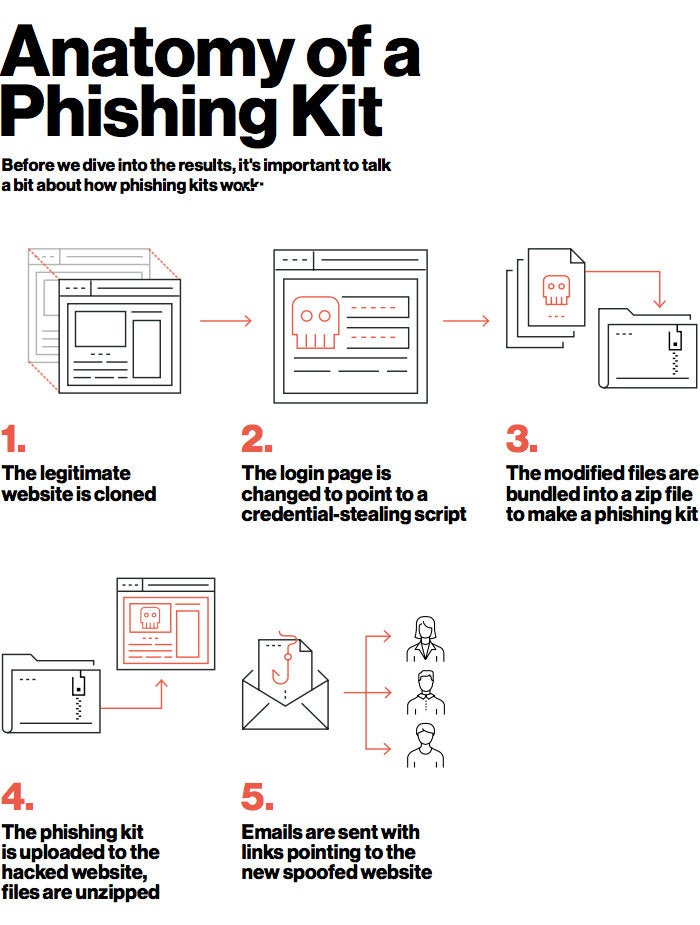
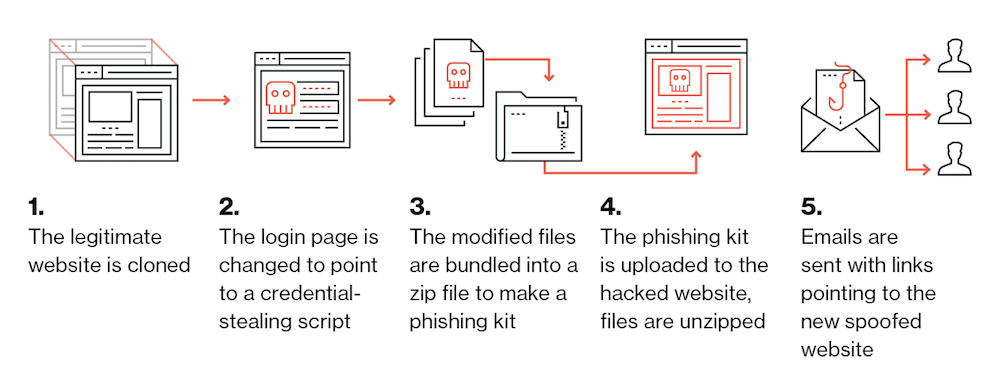
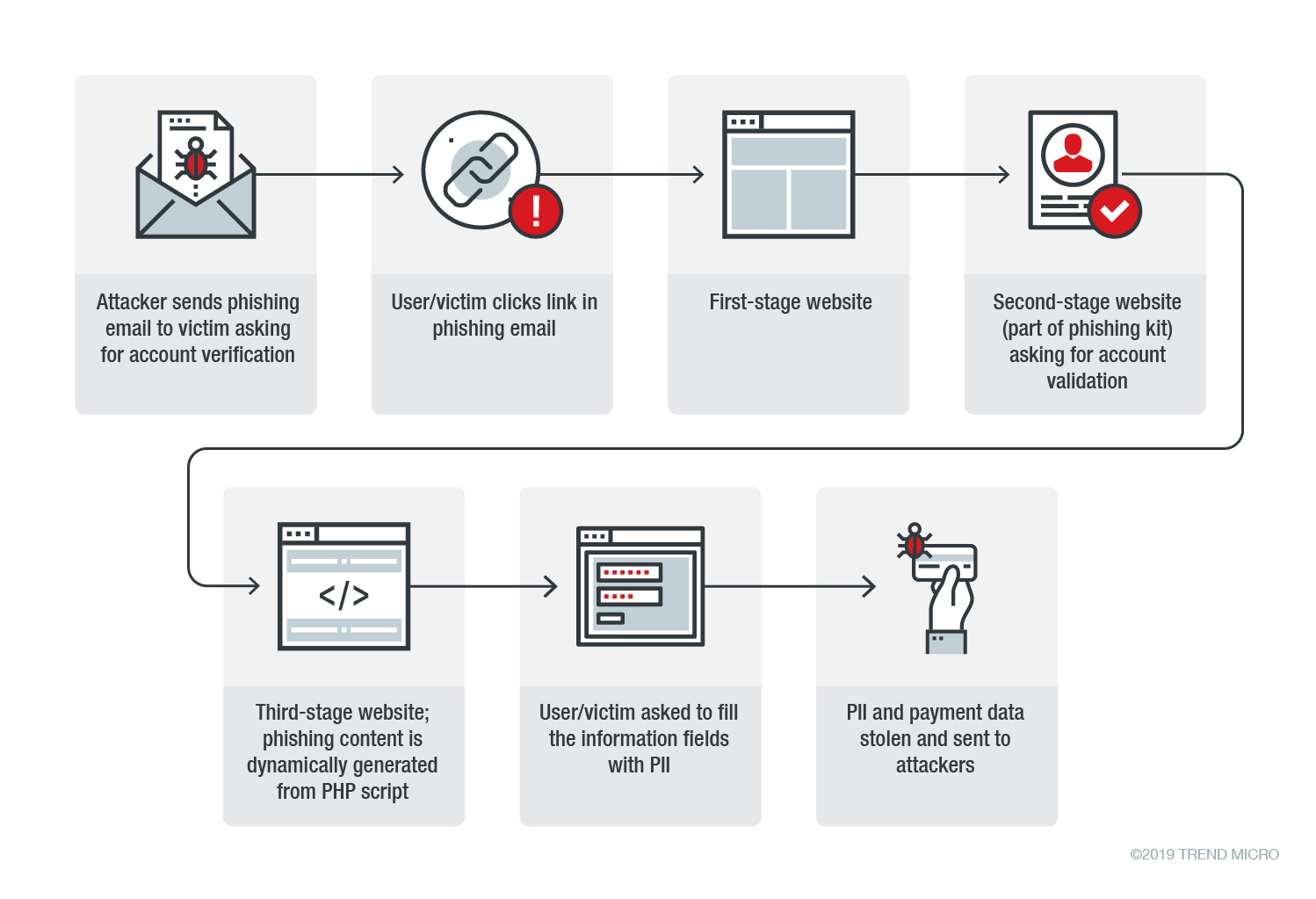
Phishing kit, per “automatizzare” le frodi informatiche: cosa sono e come proteggersi - Cyber Security 360